Myth 1: Employees won’t accept 2FA
Much of this belief stems from frequent headlines that say people are resistant to using 2FA in their personal lives. One of the most prominent stories in recent years came when a Google engineer revealed that less than 10% of people used its 2FA option, even though it had been available for 10 years.
There is evidence to suggest that the tide will turn though. Earlier this year, Google announced that it will auto-enrol 150 million users in two-step verification – a move that has the potential to change user attitudes significantly.According to recent research by 2FA specialist Duo, 2FA has already become more accepted over the last two years, with 79% of people having used it in 2021 compared to 53% in 2019. The same survey found that adoption is also 20% higher among individuals who are employed. This chimes with other research by LastPass that says that 57% of businesses around the world are already using multi-factor authentication.
This increase in usage in the workplace is only likely to continue with the spread of hybrid working. Many organisations are now busy putting measures like 2FA in place to protect remote employee access to their systems and networks.
Over the next years, 2FA is going to become the norm, rather than the exception, and an accepted part of daily working life.
Read also:
Why is Two-Factor-Autentification (2FA) so important?
Myth 2: 2FA is not a great user experience
In the past, there have been several clunky attempts at implementing 2FA in workplaces that have given it a reputation for poor user experience. Early two-factor solutions largely relied on hardware ‘tokens’ that produced one-time passwords. These days however it’s easy to send users their second authentication factor via authenticator apps on their phone or a code sent by text message. You can also deploy biometric fingerprint or facial recognition systems.
People are getting used to using facial ID in particular for everything from accessing banking services to hiring an electric scooter. Educating users that using 2FA to access workplace systems can be as seamless and easy as these experiences should not be a big step.

Myth 3: 2FA isn’t as secure as it promises to be
Try a quick Google search and you will find commentators prepared to say that 2FA isn’t completely secure. Some have pointed out that the SIM swap attack perpetrated against Twitter CEO Jack Dorsey showed how easy it is to intercept one-time codes sent to phones to change passwords and access systems. Others have highlighted bots that attackers can use to intercept one-time codes or passwords.
These attacks are relatively infrequent though. And there are solutions. For example, many security experts now advocate using hardware security keys – small USB devices that users carry with them and plug into PCs – as an alternative second factor for authentication that eliminates the possibility of codes being stolen over the air. Biometric facial recognition also provides a second layer of authentication that is more difficult to fake.
Above all, what organisations need to remember is that using 2FA in any form is vastly more secure than carrying on running with simple password access to systems. According to Microsoft, 2FA is effective at preventing 99.9% of attacks on accounts.
Organisations should also be mindful that attacks on passwords have increased throughout the pandemic. Attacks rose by 45% in a six month period in 2021 alone, prompted largely by the increase in remote working beyond corporate perimeters and the threat this poses to security
The message from all this is clear: any organisation that wants to protect critical data and systems should be considering implementing 2FA in some form and making sure employees use it…and as soon as possible.
At Admincontrol, we encourages all customers to activate 2FA on our Virtual Data Room and Board Portal solutions (free of charge) in 2022.
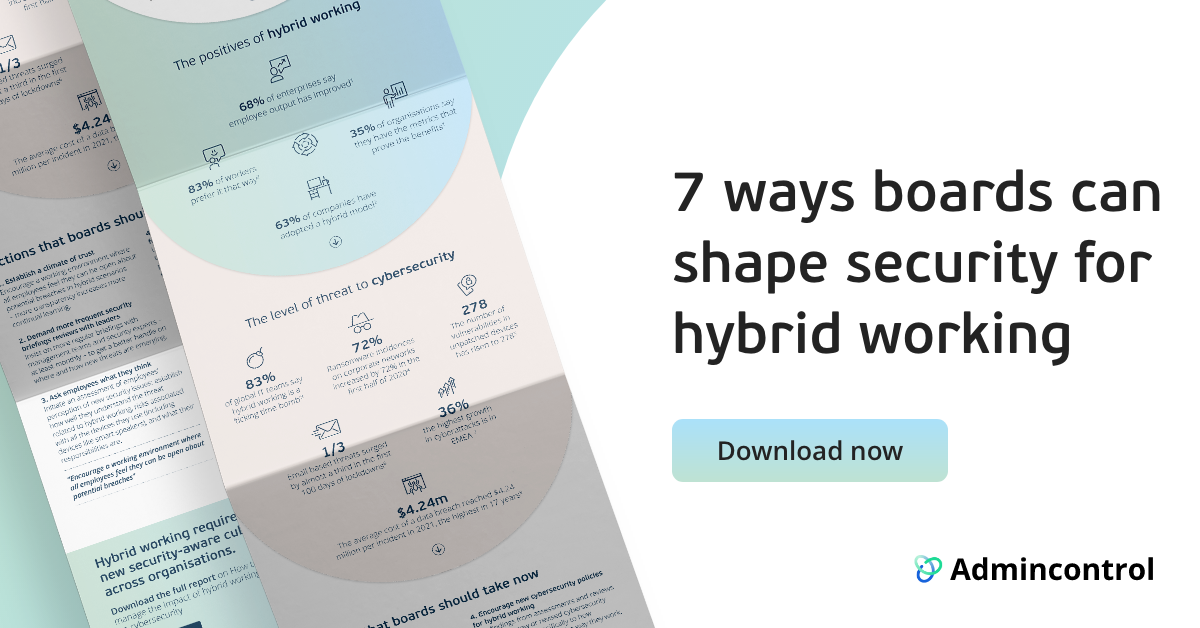
If you want to find out more about other ways you increase security, you may also be interested in our handbook on how to manage the impact of hybrid working on cybersecurity: